Manual Investigations: The Struggle Is Real
Data exfiltration refers to the unauthorized transfer of sensitive or confidential information from a network or system to an external location. This covert activity often occurs stealthily, exploiting vulnerabilities in security protocols or utilizing sophisticated malware. Data exfiltration poses significant threats to organizations, as it can lead to breaches of privacy, intellectual property theft, and financial losses. Investigating data exfiltration security alerts, particularly those triggered by analytics, can be challenging for organizations, often requiring significant amounts of time and resource effort to determine the source and extent of the breach.
Additionally, manual investigation processes can be time-consuming and subject to human error, resulting in slower response times and exacerbating the impact of breaches.
Thus, we are pleased to introduce the Cortex XDR- Large Upload playbook. This playbook is designed to streamline the management of Cortex XDR analytics “large upload” alerts, speeding the investigation process and providing efficiency and precision when confronting data exfiltration threats.
What are Large Upload alerts?
In most organizations, data exfiltration occurs via standard channels like Google, Dropbox, and smaller file-sharing sites. Since some protocols, such as HTTPS, are permitted, it is relatively straightforward to exfiltrate data. You can prevent data exfiltration by identifying large uploads that may indicate a vulnerability in your network.
Cortex XDR large upload alerts are notifications triggered by the detection of significant amounts of data being uploaded from an organization's network to an external destination. These alerts indicate potential security breaches or unauthorized data exfiltration attempts. Large upload alerts highlight anomalies in network traffic patterns, providing insights into activities that deviate from normal behavior. Such anomalies can range from a sudden surge in data transfer volumes to suspicious destinations or protocols.
The Large Upload playbook flow
The playbook investigates Cortex XDR incidents involving large upload alerts and is designed to run as a sub-playbook within Cortex XDR Alerts Handling v2. This playbook supports all Cortex XDR large upload alert types (Generic, HTTPS, FTP, SMTP). The playbook automates and streamlines the investigation process, significantly reducing the time and effort required to identify and respond to large upload alerts. Let's delve into the playbook's workflow to understand how it simplifies the investigation process.
1. Searching for similar incidents
The playbook starts by searching for similar, previous incidents that were closed as false positives. If such incidents are found and the user has set the 'FurtherInvestigation' playbook input to 'true,' the playbook intelligently skips unnecessary steps, saving both time and server resources.
2. Enrichment
To avoid wasting resources on inconsequential data, the enrichment section of the playbook first checks the volume of uploaded data against the 'Transferred_Data_Threshold' playbook input configured by the user. If the volume is below the threshold, the playbook skips ahead, ensuring efficiency. It then enriches the initiator and destination hostnames and IP addresses, the initiator username, and the SHA256 hash of the initiator file.
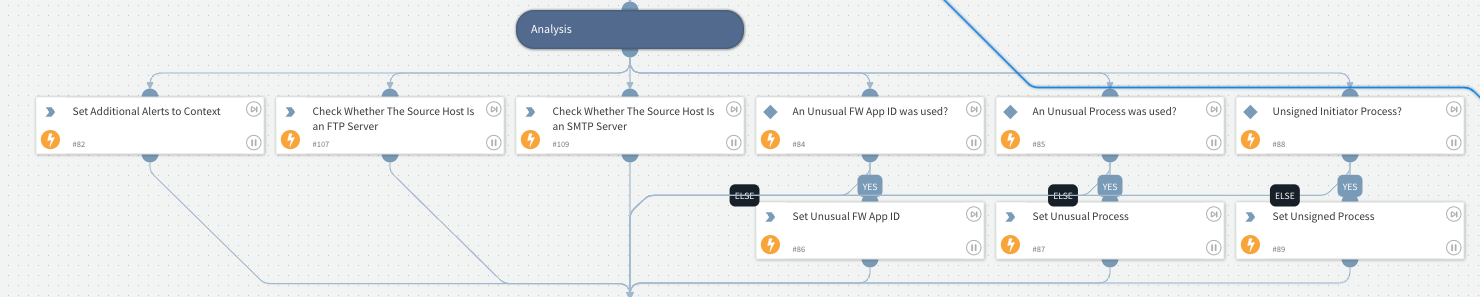
3. Analysis
As part of the analysis stage, the playbook checks for additional alerts within the investigation and checks if the initiator process is signed and if the initiator host is an FTP or SMTP server. To ensure alignment with the organization's policies, the playbook checks the name of the initiator process and the Firewall App ID associated with the traffic. The playbook compares this with the company's known and trusted App IDs and Process Names set in the 'FWApps_Processes_Whitlist' playbook input.
4. Containment
Throughout this phase of the playbook, any malicious indicators identified thus far will be blocked if the 'EarlyContainment' playbook input is set to true to limit the damage caused by the current security incident.
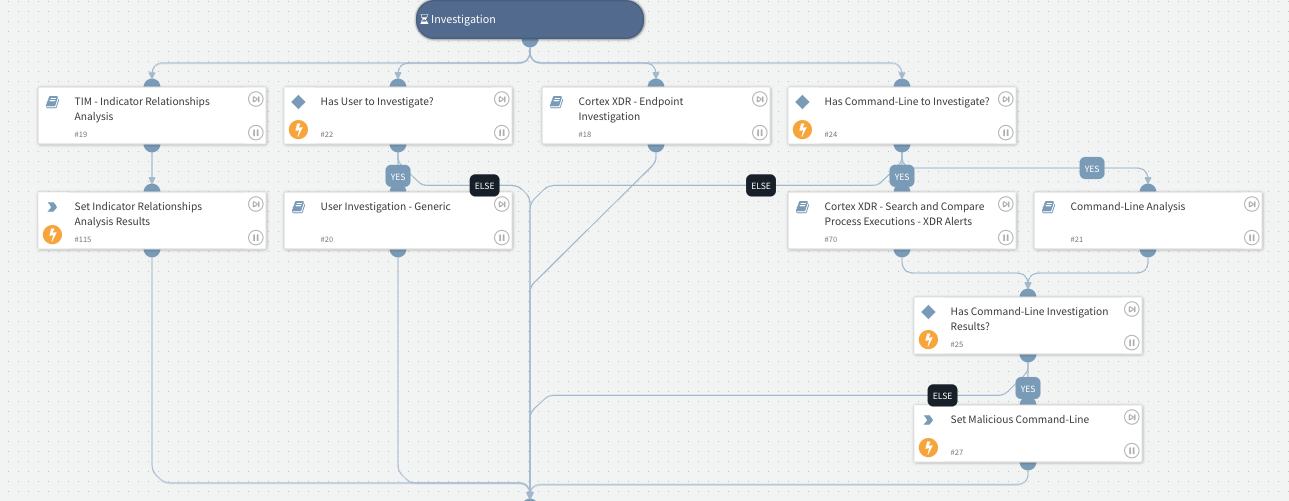
5. Investigation
To identify additional suspicious activities or alerts, the playbook investigates the initiator username, hostname, and command line to provide a comprehensive understanding of the incident. Within this stage, the playbook also detects related indicators and analyzes their relationships. This step is crucial to properly understand the broader context of the incident and identify potential patterns that may indicate malicious activity.
6. Verdict and Threat Hunting and Blocking
The alert verdict is calculated using the information gathered so far by the playbook. Threats are hunted if the alert verdict indicates malicious activity. With detected indicators, the sub-playbook conducts threat hunting and provides security teams with actionable insights. If malicious indicators are confirmed, the playbook blocks them as part of the remediation phase, preventing further compromise.
7. Remediation
Upon locating additional indicators, the playbook blocks them and isolates affected endpoints if the input for "AutoIsolateEndpoint" is set to 'true,' containing the threat and limiting its impact.
Wrapping Up: Advancing Incident Response with the Large Upload Playbook
In most organizations, data exfiltration occurs via standard channels like Google, Dropbox, and smaller file-sharing sites. Data exfiltration is relatively straightforward because some protocols, such as HTTPS, are typically permitted in organizations. Ultimately strengthening defense against evolving data exfiltration threats will result from responding quickly and decisively to potential exfiltration threats through automation and optimization of the investigation process.
Considering the sensitivity of data and the potential impact of unauthorized uploads, promptly identifying and investigating large upload alerts is paramount to maintaining a robust cybersecurity posture.
Get started on your security automation journey. Download our e-book “A Practical Guide to Deploying SecOps Automation.”