Automate Your Response to the Microsoft Outlook for Windows Vulnerability (CVE-2023-23397)
On March 14th 2023, as part of Microsoft’s Patch Tuesday release, a critical Elevation of Privilege (EoP) vulnerability in Microsoft Outlook was published, impacting Windows operating systems, with a CVSS score of 9.8. The vulnerability can lead to unauthorized access to NT (New Technology) LAN Manager (Net-NTLMv2) credentials which can be used for NTLM relay attacks against other services supporting NTLM authentication.
How Does it Work?
To successfully exploit CVE-2023-23397, an attacker can send a specially crafted email, including a UNC path delivered in an Outlook calendar invite or an appointment reminder, that will trigger, without any user interaction, a connection from the victim host to an external server controlled by the threat actor.
Once the connection is established, the attacker can steal the NTLM hashes and use them to access other network systems supporting NTLM or for offline cracking.
All supported versions of Microsoft Outlook for Windows are affected, and Microsoft has released a patch to address the vulnerability. It is strongly recommended that all customers update Microsoft Outlook for Windows to remain secure. This vulnerability does not affect other versions of Microsoft Outlook, such as Android, iOS, and Mac, as well as Outlook on the web and other Microsoft 365 services.
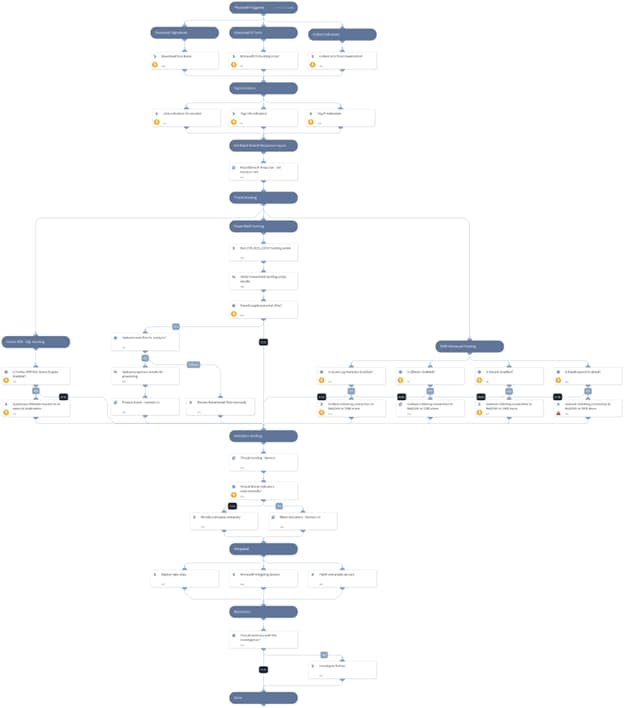
Use a Playbook for Automated Mitigation
When information continues to be published throughout the network regarding the vulnerability and its analysis, the centralization of the data while clearing what is irrelevant is essential for a quick and efficient response to the incident.
As a part of our Rapid Breach Response content pack series, the Cortex XSOAR CVE-2023-23397 - Microsoft Outlook EoP (Elevation of Privilege) pack provides a playbook that helps you collect indicators, identify suspicious emails, and process them. Furthermore, it provides Microsoft's PowerShell hunting script, which allows one to locate and delete suspicious emails.
The playbook also provides the mitigations and workarounds published for this vulnerability.
With the Microsoft Outlook EoP pack, you can streamline the following tasks:
Threat Hunting:
- Cortex XDR XQL hunting query
- Microsoft PowerShell hunting script
- Advanced SIEM hunting queries
- Indicators hunting
The Advanced SIEM hunting queries will search for Outlook initiating a connection to a WebDAV or SMB share, which according to the vulnerability analysis, might indicate an exploitation attempt of CVE-2023-23397.
Mitigations:
- Microsoft official CVE-2023-23397 patch
- Microsoft Workarounds:
- Adding users to the Protected Users Security Group
- Blocking TCP 445/SMB outbound traffic
Detection Rules:
- Yara signatures, provided by Neo23x0, can be used to detect MSG files that exploit CVE-2023-23397.
Data Enrichment:
For this playbook, we have also provided a set of data collection tasks combined with the Process Email - Generic v2 playbook to allow users to upload, process and analyze suspicious emails found during the hunting phase. Furthermore, the emails will be used for indicator and data extraction that can be used to expand your investigation.
This playbook can be triggered manually or configured as a job. A new incident should be created, and the CVE-2023-23397 - Microsoft Outlook EoP playbook and Rapid Breach Response incident type needs to be chosen.
In conclusion, it is crucial that all customers update their Microsoft Outlook for Windows to mitigate the CVE-2023-23397 vulnerability, and we hope that this playbook can help facilitate the process.
Details on the CVE-2023-23397 - Microsoft Outlook EoP Pack can be found on the Cortex Marketplace. XSOAR customers can download it directly from their Marketplace tab.
To learn more about how you can automate security operations with Cortex XSOAR, check out our virtual self-guided XSOAR Product Tour
We also host virtual and in-person events, so check here for upcoming ones.