Here’s all of the top Palo Alto Networks news from this past week.
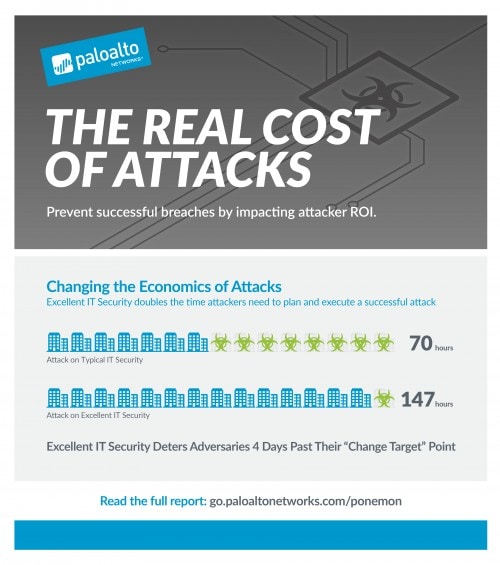
In a new study released this week, Palo Alto Networks partnered with the Ponemon Institute to understand not only what motivates cyberattackers but also how we can turn the tables on them by taking away their financial incentives to attack.
Did Operation Lotus Blossom cause Emissary Trojan Changelog to evolve? Unit 42 investigated Emissary Trojan Changelog and addressed this question.
The team also found T9000, an advanced modular backdoor that uses complex anti-analysis techniques.
Greg Day, VP & CSO, EMEA, discussed the growing role of cyber insurance.
Robert Clark reviewed "Exploding the Phone: The Untold Story of the Teenagers and Outlaws Who Hacked Ma Bell" for the Cybersecurity Canon.
The Technical Documentations team released new Traps 3.3.1 documentation.
Del Rodillas and Bryan Lee discussed why power grid security is top of mind in 2016.
Ignite is coming up soon. Find out what’s new at this year’s conference, and watch this video to find out why you don’t want miss it:
Read this week's NextWave Partner Channel Scoop.
Here are upcoming events around the world that you should know about:
Virtual Ultimate Test Drive: Next Generation Firewall
- February 8, 2016 1:00 PM - 4:00 PM CET
- Online Event
Threat Prevention Ultimate Test Drive
- February 9, 2016 10:00 AM - 3:30 PM WET
- London
Meet the CMO & Corporate Officer of Palo Alto Networks, René Bonvanie
- February 10, 2016 7:30 AM - 9:30 AM GMT+11:00
- Sydney, NSW
Meet the CMO & Corporate Officer of Palo Alto Networks, René Bonvanie
- February 10, 2016 12:00 PM - 2:30 PM GMT+10:00
- Brisbane, QLD
Palo Alto Networks Data Center Security Webinar - Middle East
- February 10, 2016 10:00 AM - 11:00 AM GMT+3:00
- Online Event
- February 10, 2016 9:00 AM - 10:00 AM PST
- Online Event
Meet the CMO & Corporate Officer of Palo Alto Networks, René Bonvanie
- February 11, 2016 5:00 PM - 6:30 PM GMT+11:00
- Melbourne, VIC
Palo Alto Networks - VMware Ortak Web Semineri
- February 11, 2016 10:00 AM - 11:00 AM EET
- Online Event
Virtual Ultimate Test Drive NGFW, Feb 11, 2016
- February 11, 2016 11:00 AM - 2:00 PM PST
- Online Event
- February 12, 2016 1:30 PM - 5:00 PM GMT+9:00
- 千代田区
Threat Prevention Ultimate Test Drive
- February 12, 2016 10:00 AM - 3:30 PM WET
- London
Virtual Ultimate Test Drive Threat Prevention, Feb 12, 2016
- February 12, 2016 11:00 AM - 2:00 PM EST
- Online Event
Virtual Ultimate Test Drive: Next Generation Firewall
- February 15, 2016 1:00 PM - 4:00 PM CET
- Online Event
- February 16, 2016 9:30 AM - 1:00 PM GMT
- London
Virtual Ultimate Test Drive Threat Prevention, Feb 16, 2016
- February 16, 2016 11:00 AM - 2:00 PM PST
- Online Event
Advanced Endpoint Protection, A Traps Tutorial
- February 17, 2016 11:00 AM - 12:00 PM PST
- Online Event
- February 17, 2016 9:00 AM - 10:00 AM PST
- Online Event
Virtual Ultimate Test Drive VDC Feb 17, 2016
- February 17, 2016 11:00 AM - 2:00 PM EST
- Online Event
Scarlet Mimic: Unit 42 Reveals Cyber Espionage Campaign
- February 17, 2016 9:00 AM - 10:00 AM PST
- Online Event
- February 18, 2016 4:00 PM - 7:30 PM GMT+9:00
- 中央区
Virtual Ultimate Test Drive NGFW Feb 18, 2016
- February 18, 2016 11:00 AM - 2:00 PM PST
- Online Event
Virtual Ultimate Test Drive Threat Prevention Feb 19, 2016
- February 19, 2016 11:00 AM - 2:00 PM EST
- Online Event
Tackle Your Toughest Security Challenges at Ignite 2016
- February 24, 2016 11:00 AM - 11:30 AM PST
- Online Event
The Cyber Attack Lifecycle in Government
- February 24, 2016 2:00 PM - 2:30 PM EST
- Online Event
Cybersecurity for Financial Services Industry
- February 25, 2016 10:00 AM - 11:15 AM GMT
- Online Event